Print Monitoring Software
See what’s being sent to the printer, control what users’ printing ability and get details and insights into printing behaviors.
Why is it important to monitor print activity?
Printers are among the most easily exploited threat vectors for threat actors, because most organizations don’t pay attention to them.
- Know anytime a user is printing sensitive data, even if they rename the file to something innocuous.
- Track who is executing print actions, which printers are used, and what was released.
- Protect against data leaks and IP theft in an often-overlooked threat vector.
- Close security gaps for data in motion.
- Enforce compliance with data handling policies or regulatory requirement and avoid hefty fines for compliance violations.
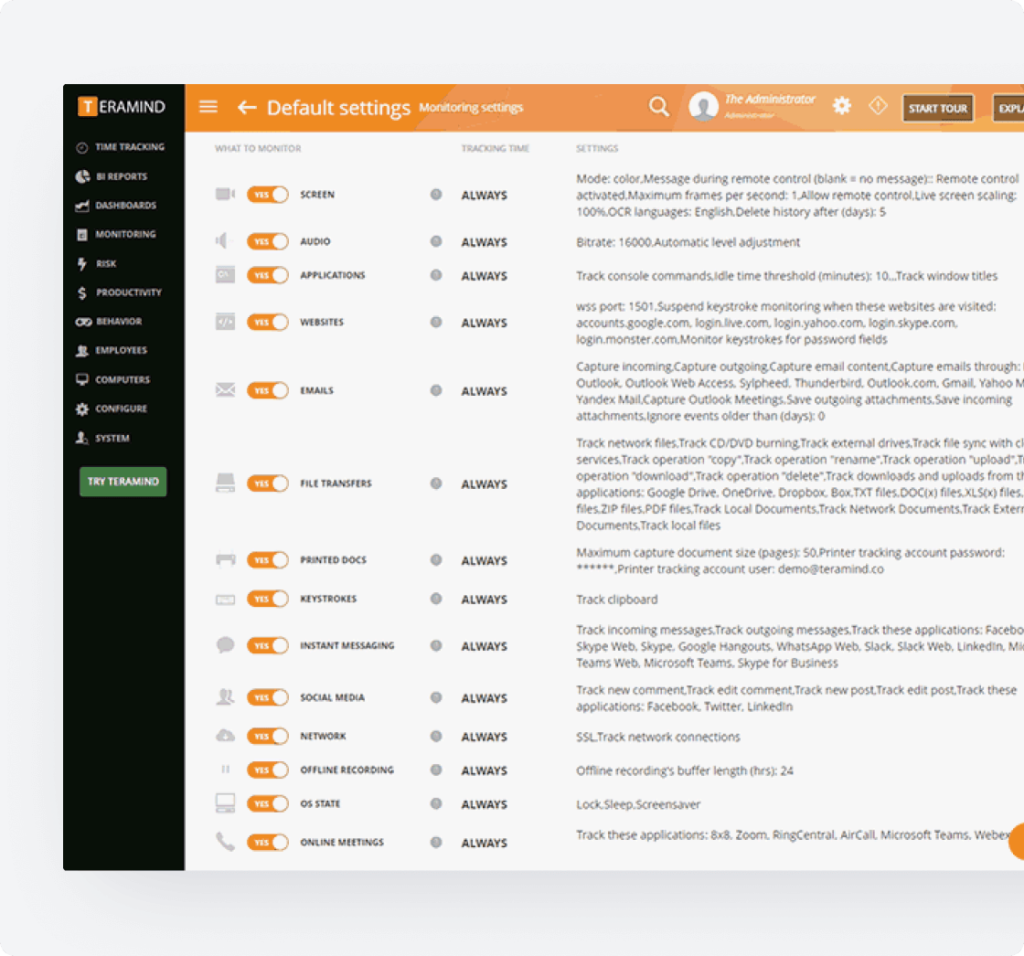
Print Tracking Features
Monitoring employee print logs is a key component of preemptively preventing sensitive data from being leaked. Teramind collects all document print requests that are made by users and administrators.
- Set alerts for the attempted printing of sensitive data.
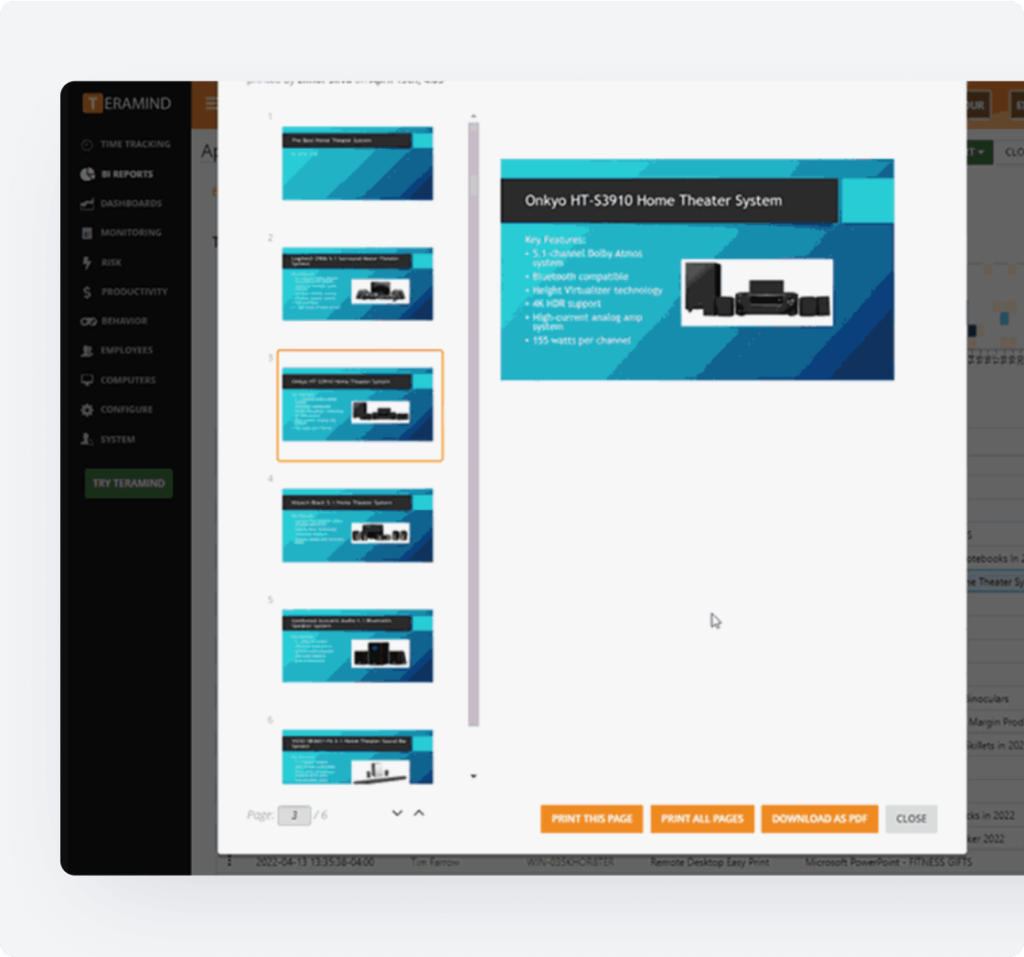
- View contents of the entire printed document.
- Find documents printed by user, computer, printer, or file name.
- Record printer usage information for security logs and audit compliance processes.
- Use screen recording for irrefutable evidence in internal investigations.
Core Teramind Features
Leverage Teramind’s unparalleled power to solve your workforce challenges.

Live View & Historical Playback
Monitor employee screens in real-time or review past activity with historical playback to gain complete visibility into user activity and computer activity.
Optical Character Recognition
Teramind’s OCR functionality allows you to extract text from images and screenshots, enhancing your monitoring and analysis capabilities.
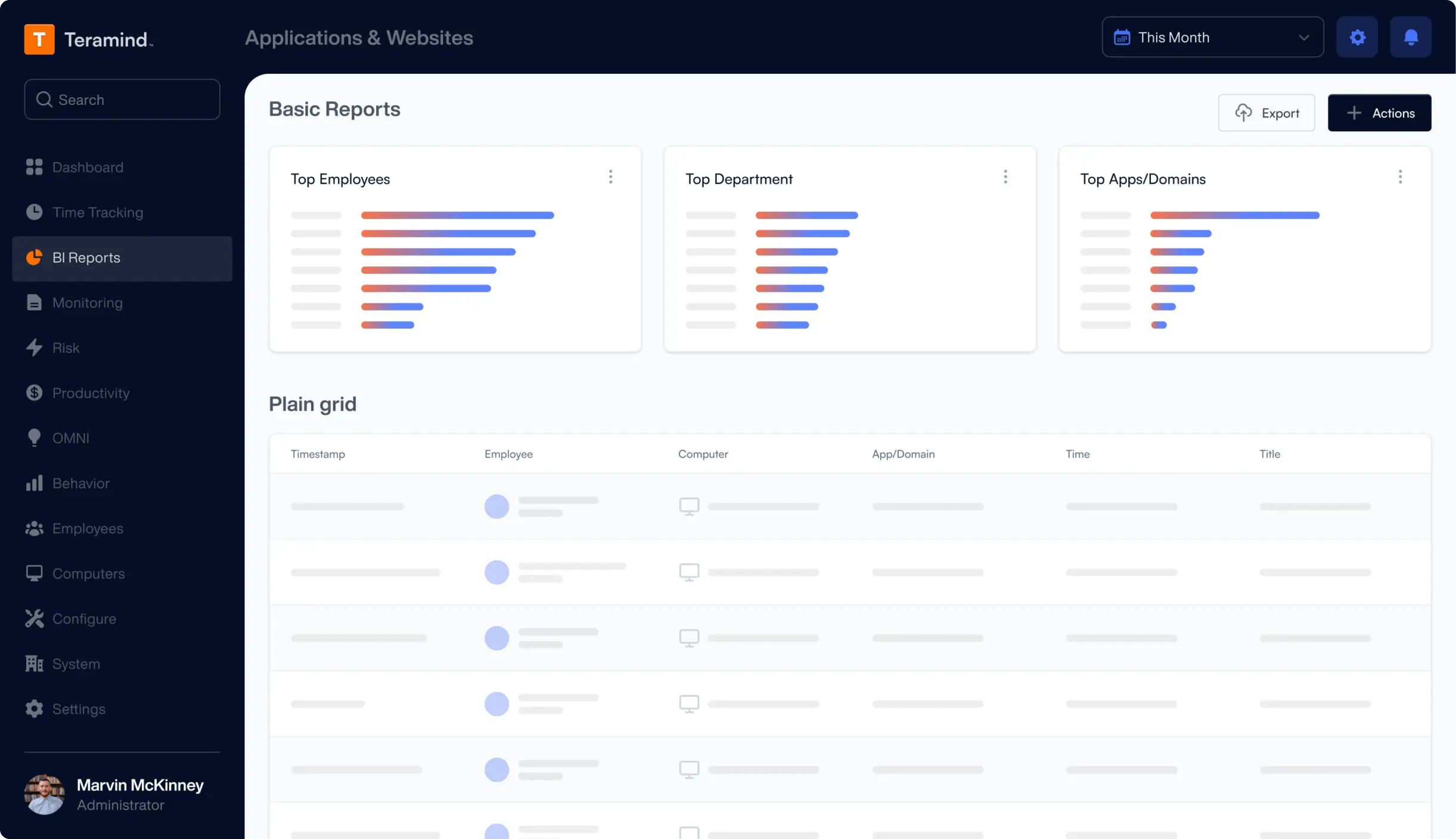
Website Monitoring
Track employee time spent on websites, identify unproductive web browsing, and enforce company policies with comprehensive website monitoring.
Application Monitoring
Monitor application usage, track time spent on specific apps, and identify potential security risks with detailed application monitoring on your endpoints.

Email Monitoring
Monitor employee emails to prevent data leaks, ensure compliance with company policies, and protect sensitive information.

Instant Message Monitoring
Track instant messages and conversations to gain insights into team communication and collaboration, and ensure compliance.

Social Media Monitoring
Monitor social media activity to protect your brand reputation, prevent data leaks, and ensure employees adhere to company policies.
Network Monitoring
Gain visibility into network activity, identify potential security threats, and optimize network performance with network monitoring.
Citrix Monitoring
Monitor employee activity within Citrix environments, track application usage, and ensure data security with specialized Citrix monitoring on your devices.

Remote Desktop Control
Take control of remote employee computers in real-time to provide support, troubleshoot issues, or prevent data breaches and insider threats.

RDP Session Recording
Record RDP sessions to gain a comprehensive understanding of user activity, troubleshoot technical problems, and ensure compliance.

Productivity Analysis
Analyze employee productivity with detailed metrics, identify areas for improvement, and boost productivity across your team members.

Active Vs. Idle Time Logs
Track active and idle time to understand how employees spend their work hours and optimize time management and productivity.

Unproductive Work Time Analysis
Identify unproductive work time, analyze patterns, and implement strategies to improve efficiency and time management.
Request Your
Custom Demo Now
What our Customers Say
Larissa H.
IT Support Specialist
Yakir D.
CIO
IT Security & Risk Manager
$7B Manufacturing Enterprise

