File Activity Monitoring
Safeguard sensitive files and protect against data loss and insider threats with behavioral insights and automated responses for file activities.
Why is it important to monitor file activity?
Monitoring file activity enables you to enhance security for data in motion:
- Prevent noncompliant file sharing in or outside of your organization.
- Identify instances of accidental or malicious data exfiltration.
- Block noncompliant handling of sensitive internal files.
- Enforce compliance with regulatory requirements and provide evidence of security controls for security assessments and audits.
Enhance your understanding of processes.
Tracking all actions taken with files also gives you the ability to watch a file as it moves from one user to another for process documentation.
- Track files as they move across users.
- Gain visibility into collaborative processes.
- Identify bottlenecks and blockers.
- Make data-based enhancements to systems.
- Improve file handling efficiency.
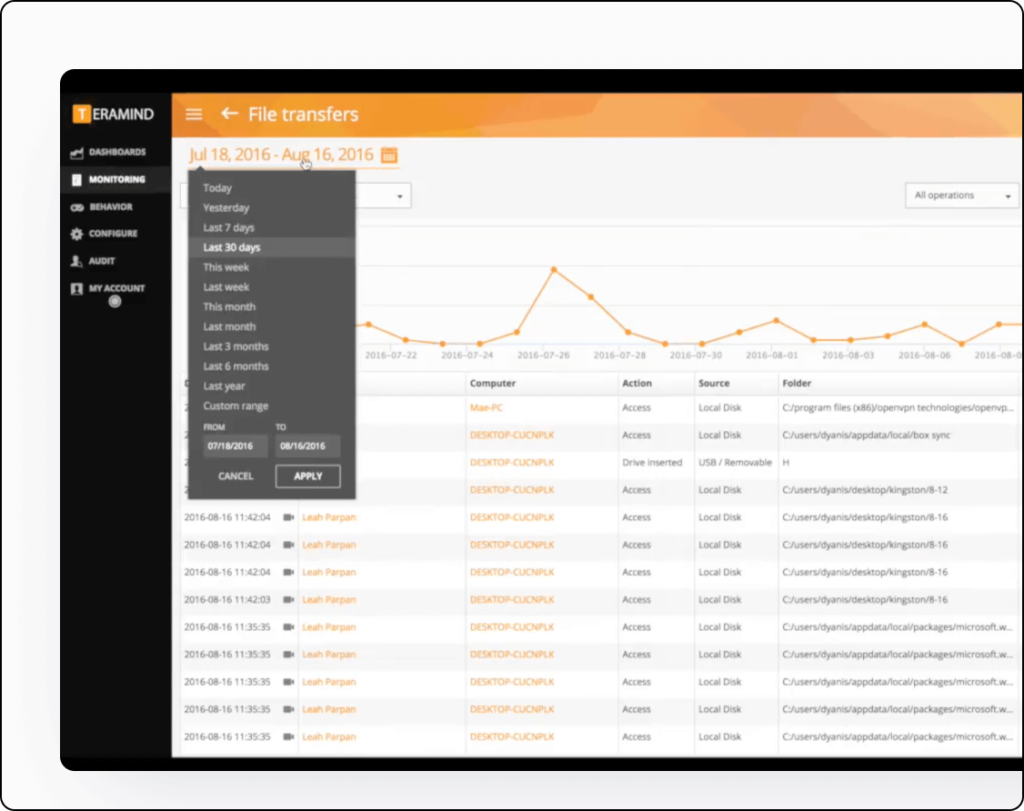
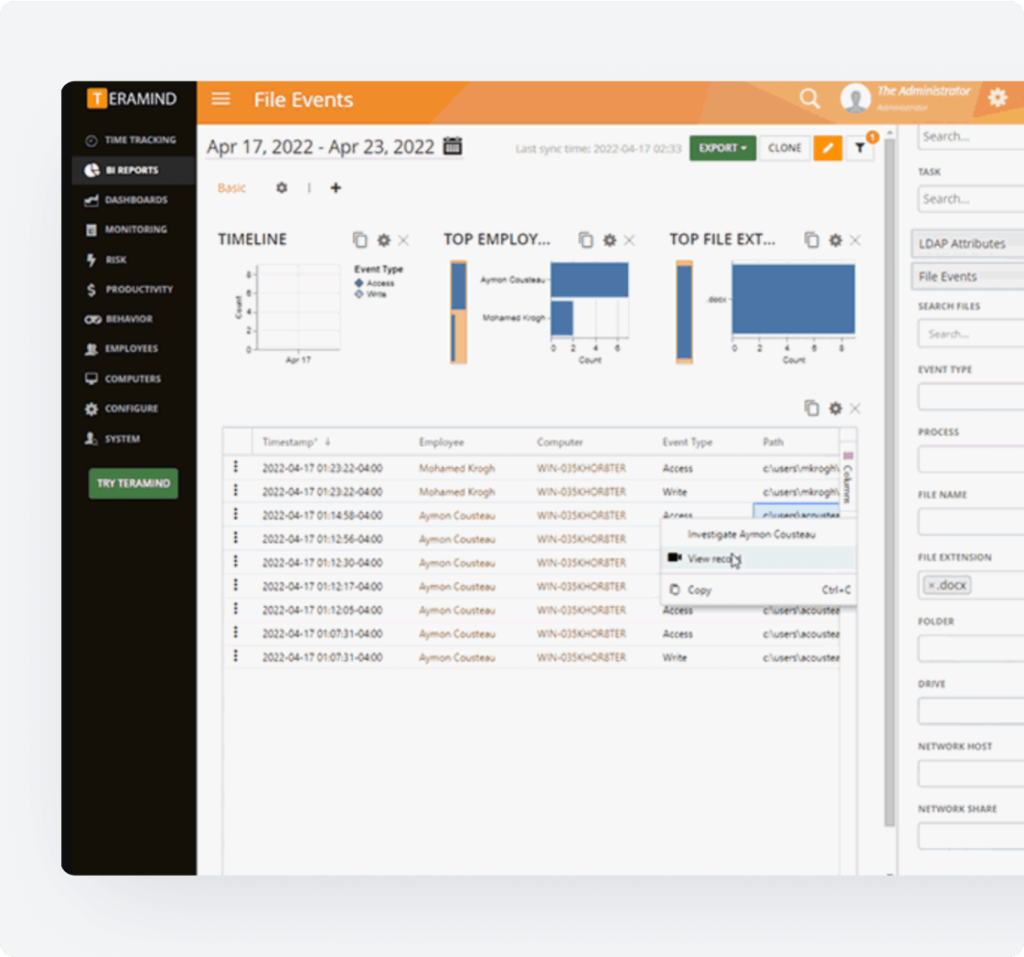
File Transfer Tracking Features
Tracking all actions taken with files also gives you the ability to watch a file as it moves from one user to another for process documentation.
- Track files as they move across users.
- Gain visibility into collaborative processes.
- Identify bottlenecks and blockers.
- Make data-based enhancements to systems.
- Improve file handling efficiency.
Development & Engineering
Core Teramind Features
Leverage Teramind’s unparalleled power to solve your workforce challenges.

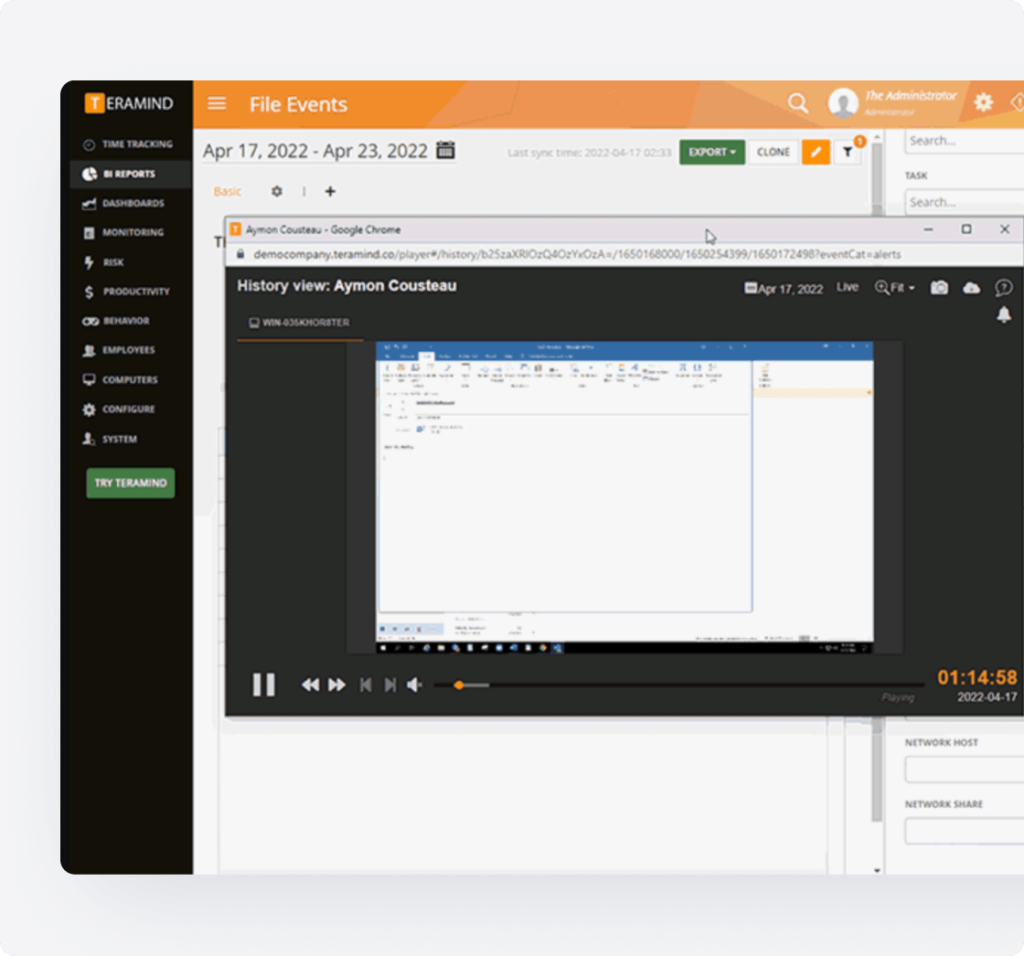
Live View & Historical Playback
Monitor employee screens in real-time or review past activity with historical playback to gain complete visibility into user activity and computer activity.
Optical Character Recognition
Teramind’s OCR functionality allows you to extract text from images and screenshots, enhancing your monitoring and analysis capabilities.
Website Monitoring
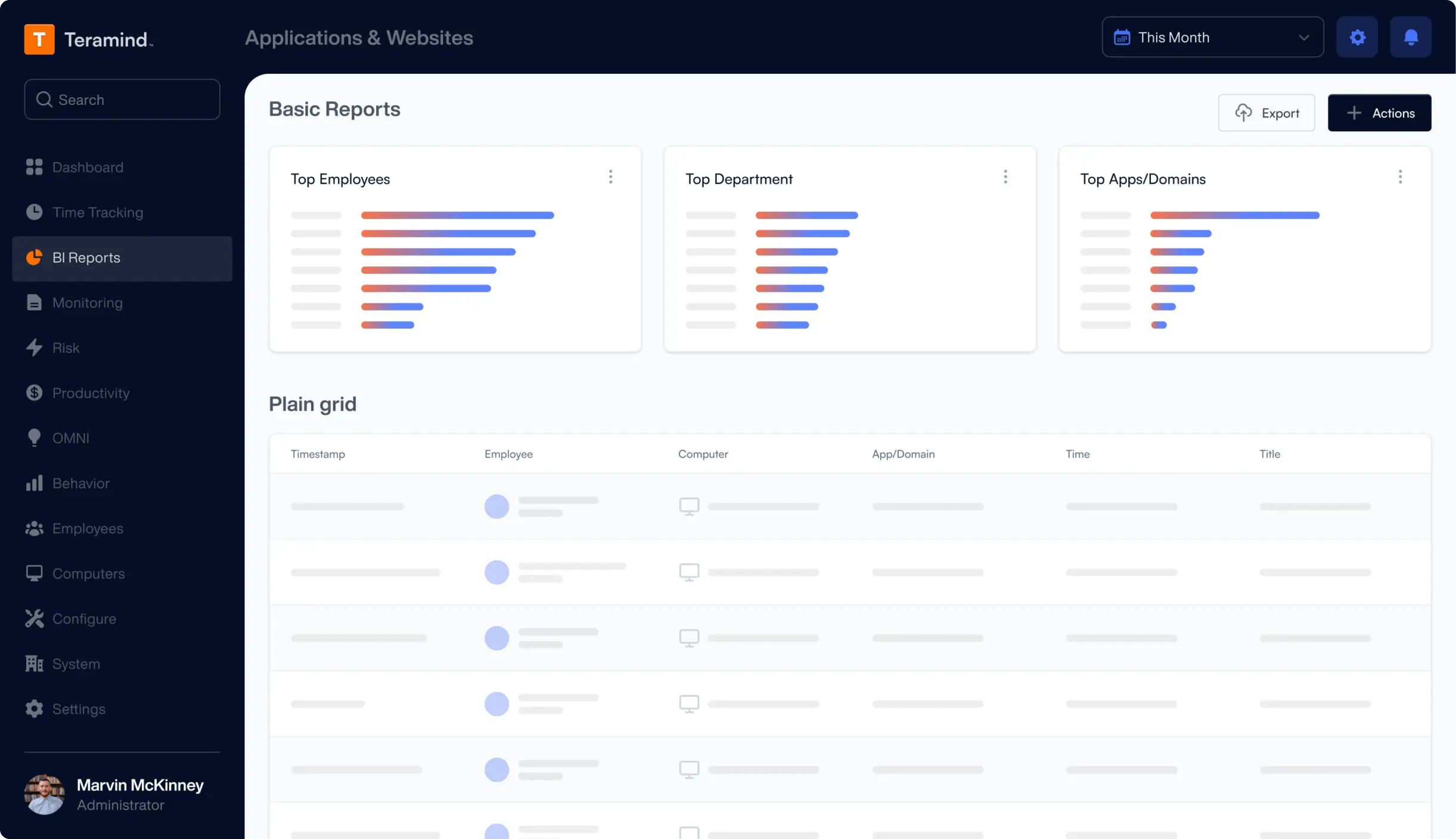
Track employee time spent on websites, identify unproductive web browsing, and enforce company policies with comprehensive website monitoring.
Application Monitoring
Monitor application usage, track time spent on specific apps, and identify potential security risks with detailed application monitoring on your endpoints.

Email Monitoring
Monitor employee emails to prevent data leaks, ensure compliance with company policies, and protect sensitive information.

Instant Message Monitoring
Track instant messages and conversations to gain insights into team communication and collaboration, and ensure compliance.

Social Media Monitoring
Monitor social media activity to protect your brand reputation, prevent data leaks, and ensure employees adhere to company policies.
Network Monitoring
Gain visibility into network activity, identify potential security threats, and optimize network performance with network monitoring.
Citrix Monitoring
Monitor employee activity within Citrix environments, track application usage, and ensure data security with specialized Citrix monitoring on your devices.

Remote Desktop Control
Take control of remote employee computers in real-time to provide support, troubleshoot issues, or prevent data breaches and insider threats.

RDP Session Recording
Record RDP sessions to gain a comprehensive understanding of user activity, troubleshoot technical problems, and ensure compliance.

Productivity Analysis
Analyze employee productivity with detailed metrics, identify areas for improvement, and boost productivity across your team members.

Active Vs. Idle Time Logs
Track active and idle time to understand how employees spend their work hours and optimize time management and productivity.

Unproductive Work Time Analysis
Identify unproductive work time, analyze patterns, and implement strategies to improve efficiency and time management.
Request Your
Custom Demo Now
What our Customers Say
Larissa H.
IT Support Specialist
Yakir D.
CIO
IT Security & Risk Manager
$7B Manufacturing Enterprise

